Checkmarx
Software Supply Chain Security
Protect your software supply chain with industry-leading application security that covers your source code, open source components, and more.

Who Needs Software Supply Chain Security (SSCS)?
The growing number of recent software supply chain attacks have made it critical for enterprises to secure their software development and deployment processes, from end to end.
%
Increase in supply-chain breaches
%
Have experienced a supply chain attack
%
Increase in malicious packages since 2022
%
of CISOs are concerned about the dangers of malicious packages
Checkmarx Secures the
Software Supply Chain
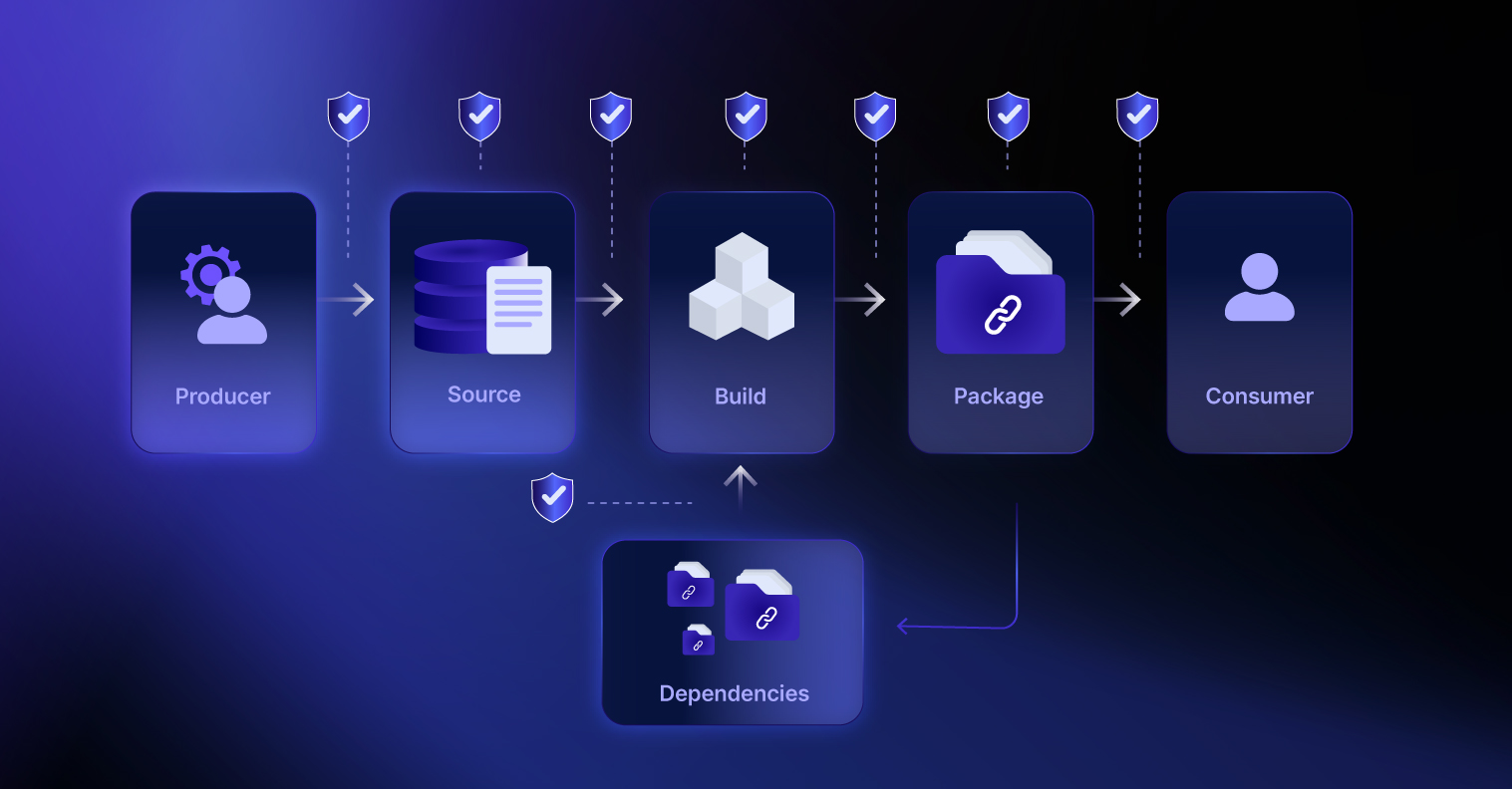
Your software supply chain contains numerous third-party components that can expose you to vulnerabilities, malicious code, and other threats. Checkmarx One helps you minimize the risk surface of your published applications by addressing every stage of the supply chain.
Checkmarx is a member of the OASIS Open Supply Chain Information Modeling (OSIM) technical committee and is reviewing relevant standardized frameworks (such as SLSA) to standardize terminology and measurements.
Why Choose Checkmarx SSCS?
Hundreds of leading enterprises trust Checkmarx’ eighteen years of AppSec experience and best-in-class SSCS solution. You should too.
Checkmarx One: A Complete SSCS Solution
Checkmarx One delivers everything your security, development and DevOps teams need to secure your software supply chain, in a single platform.
Software Composition Analysis (SCA)
Identify, prioritize and remediate security and license risks in open source libraries. Checkmarx SCA’s vulnerability detection accuracy has been independently proven to be far ahead of the competition’s.
Malicious Package Protection

Identify open source libraries that contain malicious code or exhibit suspicious behavior. Checkmarx’ malicious package database is, by far, the largest in the industry.
Remediation Prioritization & Guidance
Give your team actionable guidance to swiftly remediate the most critical threats in your software supply chain, prioritized based on multiple independent indicators.
Software Bill of Materials (SBOM)
Generate, share and ingest SBOMs in industry-standard formats, to inventory the components of your applications and more easily comply with relevant regulatory, policy, and licensing requirements.
Container Security
Simplify image scanning, Docker environment monitoring, and vulnerability detection in containers. Prioritize and remediate vulnerabilities via correlation with runtime data.
AI-Generated Code Scanning
Automatically scan AI-generated code and referenced open source libraries for vulnerabilities and malicious packages, to prevent AI-generated errors or hallucinations from harming the organization.
-
Software Composition Analysis (SCA)
Identify, prioritize and remediate security and license risks in open source libraries. Checkmarx SCA’s vulnerability detection accuracy has been independently proven to be far ahead of the competition’s.
-
Malicious Package Protection
Identify open source libraries that contain malicious code or exhibit suspicious behavior. Checkmarx’ malicious package database is, by far, the largest in the industry.
-
Remediation Prioritization & Guidance
Give your team actionable guidance to swiftly remediate the most critical threats in your software supply chain, prioritized based on multiple independent indicators.
-
Software Bill of Materials (SBOM)
Generate, share and ingest SBOMs in industry-standard formats, to inventory the components of your applications and more easily comply with relevant regulatory, policy, and licensing requirements.
-
Container Security
Simplify image scanning, Docker environment monitoring, and vulnerability detection in containers. Prioritize and remediate vulnerabilities via correlation with runtime data.
-
AI-Generated Code Scanning
Automatically scan AI-generated code and referenced open source libraries for vulnerabilities and malicious packages, to prevent AI-generated errors or hallucinations from harming the organization.

Checkmarx One
The Cloud-Native Enterprise Application Security Platform
Checkmarx One delivers a full suite of enterprise AppSec solutions in a unified, cloud-based platform that allows enterprises to secure their applications from the first line of code to deployment in the cloud.
Get everything your enterprise needs to integrate AppSec across every stage of the SDLC and build a successful AppSec program
Application Security Posture
Management (ASPM) Consolidated, correlated, prioritized insights to help your team manage risk
Code
AI Powered-
Conduct fast and accurate scans to identify risk in your custom code.
-
Eliminate shadow and zombie APls and mitigate API-specific risks.
-
Identify vulnerabilities only seen in production and assess their behavior.
Supply Chain
AI Powered-
Easily identify, prioritize, remediate, and manage open source security and license risks.
-
Catalog and track all software components to enhance security and ensure compliance.
-
Detect and remediate malicious or suspicious third-party packages that may be endangering your organization.
Cloud
AI Powered-
Scan container images, configurations, and identify open source packages and vulnerabilities preproduction and runtime.
-
Automatically scan your laC files for security vulnerabilities, compliance issues, and infrastructure misconfigurations.
Dev Enablement
-
Secure code training to upskill your developers and reduce risk from the first line of code.
-
Built to accelerate AppSec teams and help developers secure applications from the first line of code.
Services
-
Maximize ROI with prioritized technical support, metrics monitoring, and operational assistance.
-
Augment your security team with Checkmarx services to ensure the success of your AppSec program.
-
Assess the current state of your AppSec program, benchmark against peers, and get actionable next steps for improvement.
Unified Dashboard & Reporting
Application Security Posture
Management (ASPM)
Consolidated, correlated, prioritized insights to help your team manage risk
AI Powered
Code
-
SAST
Static Application Security Testing (SAST)
Conduct fast and accurate scans to identify risk in your custom code.
-
API Security
API Security
Eliminate shadow and zombie APls and mitigate API-specific risks.
-
DAST
Dynamic Application Security Testing (DAST)
Identify vulnerabilities only seen in production and assess their behavior.
Supply Chain
-
SCA
Software Composition Analysis (SCA)
Easily identify, prioritize, remediate, and manage open source security and license risks.
-
SBOM
Software Bill of Materials (SBOM)
Catalog and track all software components to enhance security and ensure compliance.
-
Malicious Package Protection
Malicious Package Protection
Detect and remediate malicious or suspicious third-party packages that may be endangering your organization.
Cloud
-
Container Security
Container Security
Scan container images, configurations, and identify open source packages and vulnerabilities preproduction and runtime.
-
IaC Security
IaC Security
Automatically scan your laC files for security vulnerabilities, compliance issues, and infrastructure misconfigurations.
What’s in it for you
How Organizations Benefit From Checkmarx SSCS
Checkmarx One provides a one-stop software supply chain security solution for your entire team:
FAQ
What is the software supply chain?
The software supply chain consists of the people, tools, components, infrastructure, activities, practices, and processes involved with the design, development, testing, deployment, and delivery of software. Software supply chain security is the discipline focused on securing every aspect of the software supply chain, to minimize the risk that accidental or intentional actions may harm an organization, its customers, its employees, or its business partners.
Why has software supply chain security become so important?
The large and ever-growing number of software supply chain security attacks over the past few years have made it critical for enterprises to invest more resources in securing their software development and deployment processes, from end to end. Modern commercial applications depend heavily on third-party open source software, which has unfortunately become a successful attack vector for lone-wolf, organized, and even state-sponsored bad actors. In addition, APIs, collaboration tools, CI/CD tools, virtualization platforms, and many other commonly used platforms have also proven susceptible to attack.
What is software composition analysis (SCA)?
Software composition analysis (SCA) solutions are designed to reduce open source software (OSS) risk, by discovering all open source libraries used by an application, and determining which ones pose danger. Basic SCA tools simply compare the OSS packages listed in manifest files with publicly available vulnerability databases, whereas more advanced SCA solutions can discover any OSS, including those referenced as dependencies of dependencies (transitive dependency scanning), in binaries (when manifest files are not available), and in private package managers. Advanced solutions can also identify malicious packages, prioritize the most important risks to mitigate first (using techniques, such as exploitable path analysis and runtime data), and provide actionable remediation guidance. Learn more here: Checkmarx SCA.
What is an SBOM?
A software bill of materials (SBOM) is a file, in an industry-standard format, that provides a formal record of the details and supply chain relationships of various components used in building software. SBOMs help organizations keep track of the OSS packages they are using, to help in threat detection and remediation. SBOMs provide software component transparency between an organization and its customers and business partners. Governments have begun mandating the use of SBOMs; for example, the US now requires SBOMs from anyone selling software to the US federal government and its agencies (Executive Order 14028). Learn more here: Checkmarx SBOM.
What are secrets?
Secrets are any private or sensitive information that an application needs to function, but that could potentially introduce an attack vector if exposed to unauthorized parties. These include credentials (such as usernames or passwords that can grant a user or system access to resources or services), API keys or tokens (unique identifiers to authorize access to an API or web service), private keys or encryption keys (such as those used to encrypt/decrypt sensitive data or secure communication protocols), and certificates (codes used to establish trust between two entities, such as between a server and a client). Secrets can be exposed in a wide variety of places, including source code, configuration files (e.g., IaC files), CI/CD pipelines, developer productivity tools, collaboration tools, wikis, and generative AI tools. To minimize potential vulnerabilities of the software supply chain, enterprises need to identify, remove, and change any secrets exposed in any non-private location.
What is OASIS Open Supply Chain Information Modeling?
Open Supply Chain Information Modeling (OSIM) is a technical committee formed by OASIS Open, the global open source and standards organization, to standardize and promote information models crucial to software supply chain security. OSIM is an information model and unifying framework that sits on top of existing SBOM data models. Its goal is to bring clarity to software supply chain partners, mitigate vulnerabilities and disruptions, and reduce security risks. Checkmarx is a member of the OSIM technical committee, alongside other industry leaders, such as Cisco, Google, IBM, Microsoft, and SAP, and the US government’s Cybersecurity and Infrastructure Security Agency (CISA).
What is the SLSA framework?
Supply-chain Levels for Software Artifacts (SLSA), pronounced “salsa”, is a cross-industry collaboration focused on improving software supply chain security, through standards and guidelines to be used by both software producers and consumers. SLSA is organized into a series of levels that describe increasing security guarantees, including tamper-resistant evidence for securing each step of the software production process, to prevent three classes of supply chain threats: source threats (e.g., unauthorized change, compromised source repo), dependency threats (e.g., compromised build or runtime dependency), and build threats (e.g., compromise build process, compromised package registry).
Get a Demo
See Checkmarx One in Action
Join the growing number of enterprises that rely on Checkmarx to secure their software supply chain .
Securing the applications driving our world